- 2 402 202 книги
- Поиск
libcats.org



Applied Cryptanalysis: Breaking Ciphers in the Real World
Mark Stamp, Richard M. LowA case-based approach to cryptanalysis that explains how and why attacks can happenApplied Cryptanalysis focuses on practical attacks on real-world ciphers. Using detailed case studies, the authors demonstrate how modern cryptographic systems are broken, and they do so with a minimum of complex mathematics and technical jargon. All major classes of attacks are covered, providing IT professionals with the knowledge necessary for effective security implementation within their organizations. Each chapter concludes with a series of problems that enables the reader to practice and fine-tune their own cryptanalysis skills. Applied Cryptanalysis can serve as a textbook for a cryptanalysis course or for independent study.The text is organized around four major themes: * Classic Crypto offers an overview of a few classical cryptosystems, introducing and illustrating the basic principles, concepts, and vocabulary. The authors then cover World War II cipher machines, specifically the German Enigma, Japanese Purple, and American Sigaba. * Symmetric Ciphers analyzes shift registers and correlation attacks, as well as attacks on three specific stream ciphers: ORYX, RC4 (as used in WEP), and PKZIP. In addition, block ciphers are studied: Hellman's Time-Memory Trade-Off attack is discussed and three specific block ciphers are analyzed in detail (CMEA, Akelarre, and FEAL). * Hash Functions presents hash function design, birthday attacks, and the "Nostradamus" attack. Then the MD4 attack is examined, which serves as a precursor for the authors' highly detailed analysis of the recent attack on MD5. * Public Key Crypto includes an overview of several public key cryptosystems including the knapsack, Diffie-Hellman, Arithmetica, RSA, Rabin cipher, NTRU, and ElGamal. Factoring and discrete log attacks are analyzed, and the recent timing attacks on RSA are discussed in detail.
Популярные книги за неделю:

Система упражнений по развитию способностей человека (Практическое пособие)
Автор: Петров Аркадий НаумовичКатегория: Путь к себе
Размер книги: 818 Kb

Сотворение мира (3-х томник)
Автор: Петров Аркадий НаумовичКатегория: Путь к себе
Размер книги: 817 Kb
Только что пользователи скачали эти книги:
Secure Data Management, 5 conf., SDM 2008
Автор: William (Editor) JonkerКатегория: CsLn_
Размер книги: 3.21 Mb
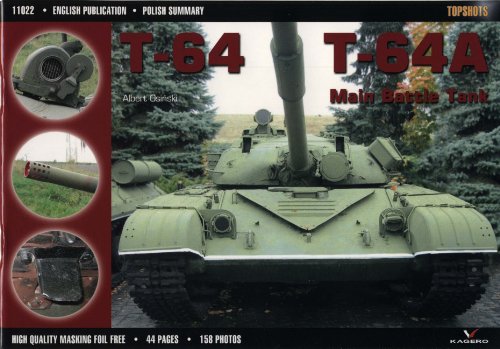
T-64, T-64A Main Battle Tank
Автор: Albert Osinski, Автор: Albert OsinskiКатегория: Вооружение
Размер книги: 8.44 Mb

Стилистика и литературное редактирование: Курс лекций
Автор: Константинова Л.А.Категория: Стилистика. Языковая норма. Культура речи
Размер книги: 2.49 Mb
Мотивация труда педагогов
Автор: Бакурадзе А.Б.Категория: Народное образование. Педагогика
Размер книги: 941 Kb






