- 2 402 202 книги
- Поиск
libcats.org




Google Hacking for Penetration Testers
Long J., Skoudis E., van Eijkelenborg A.Google, the most popular search engine worldwide, provides web surfers with an easy-to-use guide to the Internet, with web and image searches, language translation, and a range of features that make web navigation simple enough for even the novice user. What many users don't realize is that the deceptively simple components that make Google so easy to use are the same features that generously unlock security flaws for the malicious hacker. Vulnerabilities in website security can be discovered through Google hacking, techniques applied to the search engine by computer criminals, identity thieves, and even terrorists to uncover secure information. This book beats Google hackers to the punch, equipping web administrators with penetration testing applications to ensure their site is invulnerable to a hacker's search.Penetration Testing with Google Hacks explores the explosive growth of a technique known as "Google Hacking. When the modern security landscape includes such heady topics as "blind SQL injection" and "integer overflows," it's refreshing to see such a deceptively simple tool bent to achieve such amazing results; this is hacking in the purest sense of the word. Readers will learn how to torque Google to detect SQL injection points and login portals, execute port scans and CGI scans, fingerprint web servers, locate incredible information caches such as firewall and IDS logs, password databases, SQL dumps and much more - all without sending a single packet to the target! Borrowing the techniques pioneered by malicious "Google hackers," this talk aims to show security practitioners how to properly protect clients from this often overlooked and dangerous form of informationleakage.*First book about Google targeting IT professionals and security leaks through web browsing.*Author Johnny Long, the authority on Google hacking, will be speaking about "Google Hacking" at the BlackHat 2004 Briefing. His presentation on penetrating security flaws with Google is expected to create a lot of buzz and exposure for the topic.*Johnny Long's Web site hosts the largest repository of Google security exposures and is the most popular destination for security professionals who want to learn about the dark side of Google.
Популярные книги за неделю:
Тестирование Дот Ком, или Пособие по жестокому обращению с багами в интернет-стартапах
Автор: Роман Савин
Размер книги: 5.26 Mb

Система упражнений по развитию способностей человека (Практическое пособие)
Автор: Петров Аркадий НаумовичКатегория: Путь к себе
Размер книги: 818 Kb
C++ Design Patterns and Derivatives Pricing
Автор: M. S. JoshiКатегория: F_Finance, FN_Numerical
Размер книги: 748 Kb
Только что пользователи скачали эти книги:

Галина Федорова, Михаил Федоров. Будни разведки (Воспоминания нелегалов)
Автор:
Размер книги: 521 Kb

Галина Зеленина. Положение иудеев в христианском обществе по данным фуэро Сепульведы 1300-го года
Автор:
Размер книги: 17 Kb
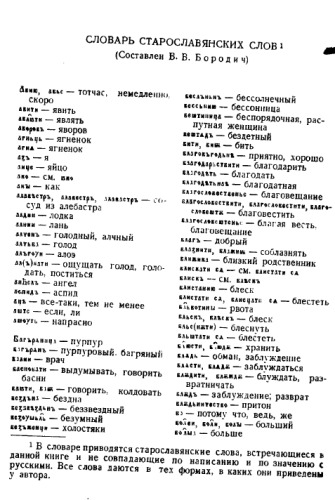
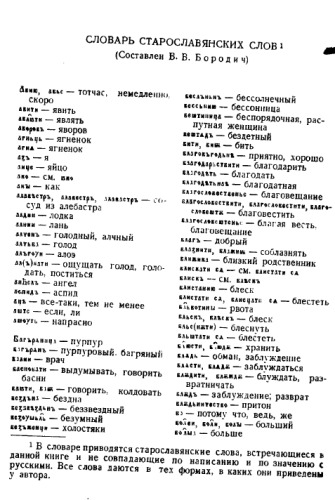
Старославянский словарь
Автор: БородичКатегория: Лингвистика, Компаративистика, Индоевропеистика, Славистика, Старославянский + История русского языка
Размер книги: 835 Kb
Representation of Lie Groups and Special Functions: Volume 1: Simplest Lie Groups, Special Functions and Integral Transforms (Mathematics and its Applications)
Автор: N.Ja. Vilenkin, Автор: A.U. KlimykКатегория: Математика
Размер книги: 6.99 Mb
Psychological Testing: Principles, Applications, and Issues
Автор: Robert M. Kaplan, Автор: Dennis P. Saccuzzo
Размер книги: 4.07 Mb

Терминология поршневых двигателей внутреннего сгорания.
Автор: Ответственный редактор А.М.Терпигорев.
Размер книги: 828 Kb





